Abstract
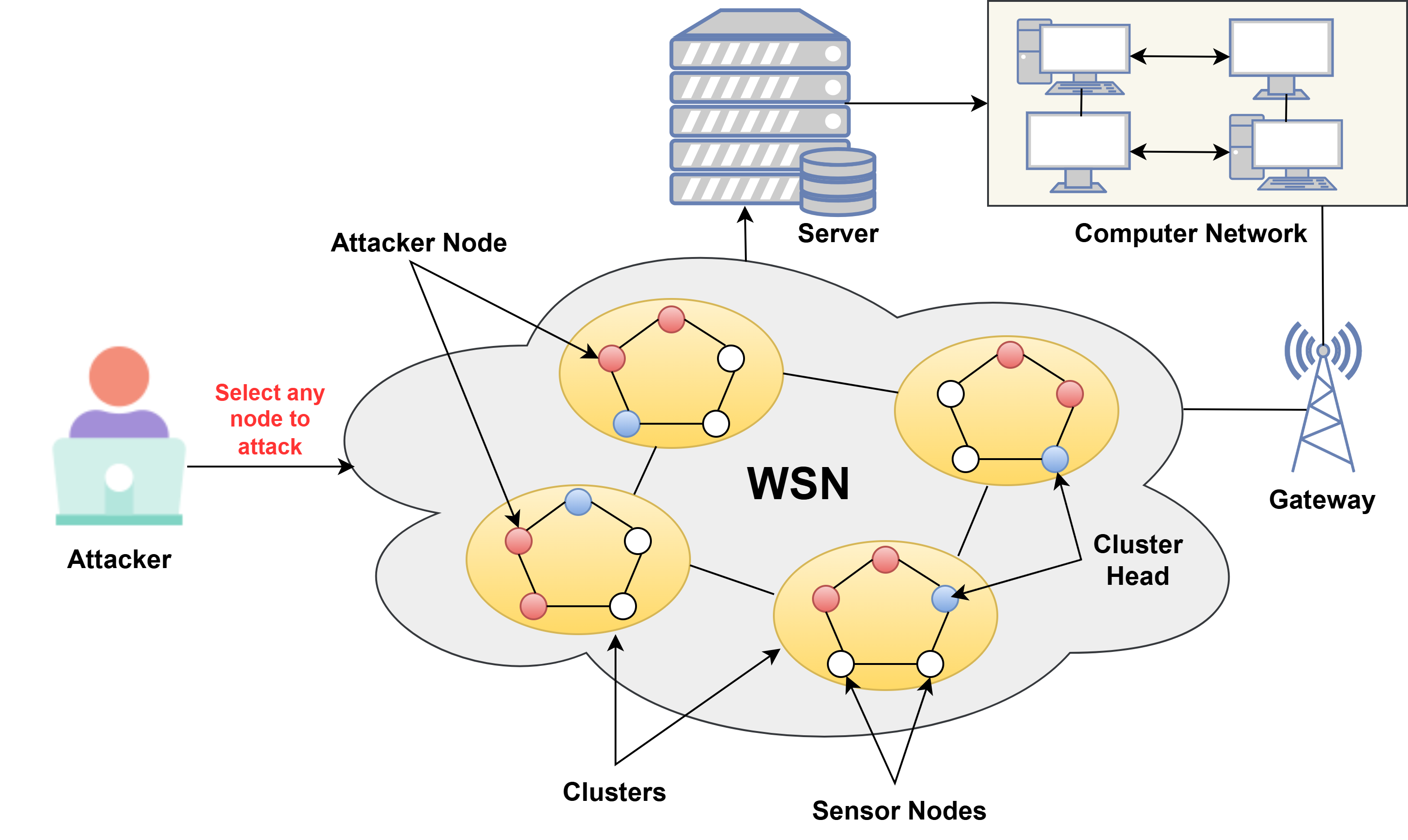
Wireless Sensor Networks (WSNs) are prone to different security threats because of their open communication environment, distributed architecture, and resource constraints. For the security and integrity of a network to be ensured, robust intrusion detection systems (IDS) are required. The WSN-DS dataset has been used to provide an effective machine learning (ML) and Deep Learning (DL) based IDS and attack detection technique for WSNs. Several learning models, including K-Nearest Neighbors (KNN), Random Forest (RF), Decision Tree (DT), Convolutional Neural Networks (CNN), Support Vector Machine (SVM), Logistic Regression (LR), and Neural Networks (NN), are compared in terms of performance. Preprocessing methods of data encoding, normalization, and data splitting are applied to the dataset to improve classification performance. The effectiveness of these models is compared using large trials with significant performance metrics such as ROC-AUC, F1-score, accuracy, precision, and recall. The results indicate that the Optimized RF model has been optimized to achieve the optimal accuracy of 99.71\%, which outperforms other state-of-the-art approaches. Apart from pointing out the importance of ML in detecting WSN attacks, this research provides a promising way forward for enhancing network security through effective detection methods.
Keywords
wireless sensor networks
intrusion detection system
security
machine learning
deep learning
WSN-DS dataset
Data Availability Statement
Data will be made available on request.
Funding
This work was supported without any funding.
Conflicts of Interest
The authors declare no conflicts of interest.
Ethical Approval and Consent to Participate
Not applicable.
Cite This Article
APA Style
Sharma, A., & Rani, S. (2025). An Optimized Ensemble Approach for Securing Wireless Sensor Networks Against Attacks. ICCK Transactions on Wireless Networks, 1(1), 5–15. https://doi.org/10.62762/TWN.2025.109626
Publisher's Note
ICCK stays neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Copyright © 2025 by the Author(s). Published by Institute of Central Computation and Knowledge. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (
https://creativecommons.org/licenses/by/4.0/), which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if changes were made.


 Submit Manuscript
Edit a Special Issue
Submit Manuscript
Edit a Special Issue
 Copyright © 2025 by the Author(s). Published by Institute of Central Computation and Knowledge. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/), which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if changes were made.
Copyright © 2025 by the Author(s). Published by Institute of Central Computation and Knowledge. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/), which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if changes were made. 