Chinese Journal of Information Fusion
ISSN: 2998-3371 (Online) | ISSN: 2998-3363 (Print)
Email: [email protected]
 Submit Manuscript
Edit a Special Issue
Submit Manuscript
Edit a Special Issue
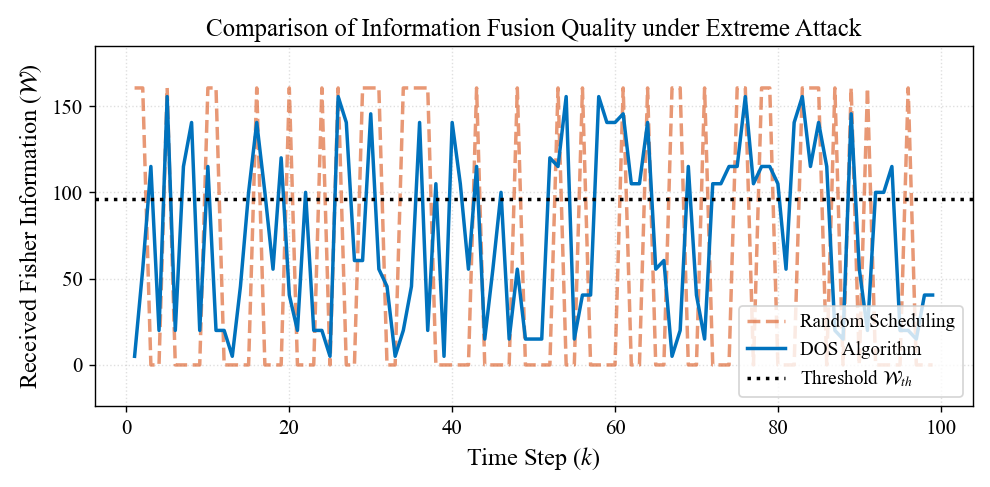
TY - JOUR AU - Lu, Jie AU - Lin, Wenhao AU - Yang, Chao PY - 2026 DA - 2026/03/06 TI - Sequential Information Fusion for Resilient Estimation: Dynamic Observation Scheduling against Intermittent DoS Attacks JO - Chinese Journal of Information Fusion T2 - Chinese Journal of Information Fusion JF - Chinese Journal of Information Fusion VL - 3 IS - 1 SP - 46 EP - 61 DO - 10.62762/CJIF.2025.922221 UR - https://www.icck.org/article/abs/CJIF.2025.922221 KW - dynamic observation scheduling KW - fisher information KW - information fusion KW - intermittent DoS attacks AB - In this paper, we consider the state estimation problem in a cyber-physical system (CPS) against intermittent denial-of-service (DoS) attacks, which are usually difficult to defend due to their concealment and unpredictability. To address this issue, this paper proposes a dynamic observation scheduling method based on Fisher information to achieve efficient and resilient state estimation. Specifically, a sliding window mechanism is first employed to predict the successful transmission probability for each time window. Subsequently, the method constructs a scheduling sequence by aligning these predicted probabilities with the Fisher information of the observation's components. This strategy effectively achieves the co-optimization of message quality and transmission risk. Theoretical analysis shows that the scheduling method can be viewed as a risk-avoidance weighted maximization problem, which can achieve single-step optimality through same-direction matching. Simulations compare the proposed approach with fixed-order and random scheduling strategies. The results show that the proposed algorithm significantly improves the estimation accuracy under standard attacks and maintains effective estimation even under extreme attacks. SN - 2998-3371 PB - Institute of Central Computation and Knowledge LA - English ER -
@article{Lu2026Sequential,
author = {Jie Lu and Wenhao Lin and Chao Yang},
title = {Sequential Information Fusion for Resilient Estimation: Dynamic Observation Scheduling against Intermittent DoS Attacks},
journal = {Chinese Journal of Information Fusion},
year = {2026},
volume = {3},
number = {1},
pages = {46-61},
doi = {10.62762/CJIF.2025.922221},
url = {https://www.icck.org/article/abs/CJIF.2025.922221},
abstract = {In this paper, we consider the state estimation problem in a cyber-physical system (CPS) against intermittent denial-of-service (DoS) attacks, which are usually difficult to defend due to their concealment and unpredictability. To address this issue, this paper proposes a dynamic observation scheduling method based on Fisher information to achieve efficient and resilient state estimation. Specifically, a sliding window mechanism is first employed to predict the successful transmission probability for each time window. Subsequently, the method constructs a scheduling sequence by aligning these predicted probabilities with the Fisher information of the observation's components. This strategy effectively achieves the co-optimization of message quality and transmission risk. Theoretical analysis shows that the scheduling method can be viewed as a risk-avoidance weighted maximization problem, which can achieve single-step optimality through same-direction matching. Simulations compare the proposed approach with fixed-order and random scheduling strategies. The results show that the proposed algorithm significantly improves the estimation accuracy under standard attacks and maintains effective estimation even under extreme attacks.},
keywords = {dynamic observation scheduling, fisher information, information fusion, intermittent DoS attacks},
issn = {2998-3371},
publisher = {Institute of Central Computation and Knowledge}
}
 Copyright © 2026 by the Author(s). Published by Institute of Central Computation and Knowledge. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/), which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if changes were made.
Copyright © 2026 by the Author(s). Published by Institute of Central Computation and Knowledge. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/), which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if changes were made. Chinese Journal of Information Fusion
ISSN: 2998-3371 (Online) | ISSN: 2998-3363 (Print)
Email: [email protected]

Portico
All published articles are preserved here permanently:
https://www.portico.org/publishers/icck/