TinyML Driven Intrusion Detection for 5G Network Slices with Leakage-Free Validation
Article Information
Abstract
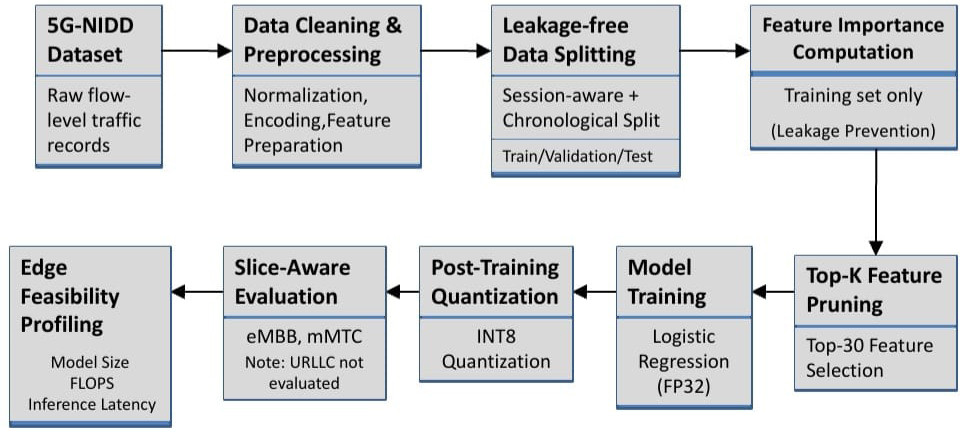
The intrusion detection at the 5G network perimeter demands learning frameworks that are practically feasible and computationally efficient. This research proposes a lightweight, slice-sensitive intrusion detection approach designed for edge deployment, with a strong emphasis on minimizing information leakage while accounting for the resource constraints inherent in edge environments. A rigorous chronological and session-discontinuous experimental protocol ensures that training and test traffic remain temporally separated, faithfully replicating realistic deployment conditions. The proposed framework employs a classical Logistic Regression classifier using flow-based statistical features extracted from the 5G-NIDD dataset. To reduce model complexity while preserving detection performance, feature importance-based pruning is applied to retain only the most informative features, followed by post-training INT8 quantization. Rather than focusing on hardware-specific implementations, edge feasibility is assessed through software-based metrics, including model size, computational cost per inference, and CPU inference latency. Experimental results demonstrate that the optimized model exhibits stable intrusion detection performance under leakage-free conditions, achieving results largely comparable to—and in some cases slightly superior to—the full-feature baseline. Notable improvements in memory footprint and computational overhead are achieved, resulting in inference latencies of less than one millisecond in software simulations. Slice-wise analysis reveals predictable and interpretable behavior for both enhanced Mobile Broadband (eMBB) and massive Machine-Type Communications (mMTC) traffic, while conclusions regarding Ultra-Reliable Low-Latency Communications (URLLC) traffic are drawn cautiously due to insufficient representation in the dataset. These findings suggest that carefully constrained classical models, combined with feature-based optimization and strict evaluation protocols, provide a practical and transparent foundation for slice-aware intrusion detection at the 5G edge.
Graphical Abstract
Keywords
Data Availability Statement
Funding
Conflicts of Interest
AI Use Statement
Ethical Approval and Consent to Participate
References
- Bouke, M. A., & Abdullah, A. (2024). An empirical assessment of ML models for 5G network intrusion detection: A data leakage-free approach. e-Prime-Advances in Electrical Engineering, Electronics and Energy, 8, 100590.
[CrossRef] [Google Scholar] - Imanbayev, A., Tynymbayev, S., Odarchenko, R., Gnatyuk, S., Berdibayev, R., Baikenov, A., & Kaniyeva, N. (2022). Research of machine learning algorithms for the development of intrusion detection systems in 5G mobile networks and beyond. Sensors, 22(24), 9957.
[CrossRef] [Google Scholar] - Buyuktanir, B., Altinkaya, Ş., Karatas Baydogmus, G., & Yildiz, K. (2025). Federated learning in intrusion detection: advancements, applications, and future directions. Cluster Computing, 28(7), 473.
[CrossRef] [Google Scholar] - Ahmad, Z., Khan, A. S., Shiang, C. W., Abdullah, J., & Ahmad, F. (2020). Network intrusion detection system: A systematic study of machine learning and deep learning approaches. Transactions on Emerging Telecommunications Technologies, 32(1), e4150.
[CrossRef] [Google Scholar] - Bocu, R., & Iavich, M. (2022). Real-time intrusion detection and prevention system for 5G and beyond software-defined networks. Symmetry, 15(1), 110.
[CrossRef] [Google Scholar] - Malik, S., & Bera, S. (2024, July). Security-as-a-function in 5g network: Implementation and performance evaluation. In 2024 International Conference on Signal Processing and Communications (SPCOM) (pp. 1-5). IEEE.
[CrossRef] [Google Scholar] - Kim, H. J., Lee, J., Park, C., & Park, J. G. (2022, October). Network anomaly detection based on domain adaptation for 5g network security. In 2022 13th International Conference on Information and Communication Technology Convergence (ICTC) (pp. 976-980). IEEE.
[CrossRef] [Google Scholar] - Silva, R. S., Meixner, C. C., Guimaraes, R. S., Diallo, T., Garcia, B. O., de Moraes, L. F., & Martinello, M. (2020). REPEL: A strategic approach for defending 5G control plane from DDoS signalling attacks. IEEE Transactions on Network and Service Management, 18(3), 3231-3243.
[CrossRef] [Google Scholar] - Yadav, N., Pande, S., Khamparia, A., & Gupta, D. (2022). Intrusion detection system on IoT with 5G network using deep learning. Wireless Communications and Mobile Computing, 2022(1), 9304689.
[CrossRef] [Google Scholar] - Shabir, M. Y., Torta, G., & Damiani, F. (2025). TinyML model compression: A comparative study of pruning and quantization on selected standard and custom neural networks. Telecommunication Systems, 88(4), 1-21.
[CrossRef] [Google Scholar] - Heydari, S., & Mahmoud, Q. H. (2025). Tiny machine learning and on-device inference: A survey of applications, challenges, and future directions. Sensors, 25(10), 3191.
[CrossRef] [Google Scholar] - Dangi, R., Jadhav, A., Choudhary, G., Dragoni, N., Mishra, M. K., & Lalwani, P. (2022). Ml-based 5g network slicing security: A comprehensive survey. Future Internet, 14(4), 116.
[CrossRef] [Google Scholar] - Akpan, V. A., Njoku, E. C., & Obi, E. I. (2025). Slice-specific machine learning models for intrusion detection in 5G telecommunication networks. International Journal of Wireless Communications and Mobile Computing, 12(2), 93-118.
[CrossRef] [Google Scholar] - Hozouri, A., Mirzaei, A., & Effatparvar, M. (2025). A comprehensive survey on intrusion detection systems with advances in machine learning, deep learning and emerging cybersecurity challenges. Discover Artificial Intelligence, 5(1), 314.
[CrossRef] [Google Scholar] - Dutta, A., & Hammad, E. (2020, September). 5G security challenges and opportunities: A system approach. In 2020 IEEE 3rd 5G world forum (5GWF) (pp. 109-114). IEEE.
[CrossRef] [Google Scholar] - Pepito, R., & Dutta, A. (2021). Open source 5G security testbed for edge computing. In 2021 IEEE 4th 5G World Forum (5GWF) (pp. 388-393). IEEE.
[CrossRef] [Google Scholar] - Ferrag, M. A., Maglaras, L., Moschoyiannis, S., & Janicke, H. (2020). Deep learning for cyber security intrusion detection: Approaches, datasets, and comparative study. Journal of Information Security and Applications, 50, 102419.
[CrossRef] [Google Scholar] - Ray, P. P. (2022). A review on TinyML: State-of-the-art and prospects. Journal of King Saud University-Computer and Information Sciences, 34(4), 1595-1623.
[CrossRef] [Google Scholar] - Mirsky, Y., Doitshman, T., Elovici, Y., & Shabtai, A. (2018). Kitsune: An ensemble of autoencoders for online network intrusion detection. Proceedings of the Network and Distributed Systems Security Symposium (NDSS), 1-15.
[CrossRef] [Google Scholar] - Moustafa, N., & Slay, J. (2016). The evaluation of Network Anomaly Detection Systems: Statistical analysis of the UNSW-NB15 data set and the comparison with the KDD99 data set. Information Security Journal: A Global Perspective, 25(1-3), 18-31.
[CrossRef] [Google Scholar] - Sultana, N., Chilamkurti, N., Peng, W., & Alhadad, R. (2019). Survey on SDN based network intrusion detection system using machine learning approaches. Peer-to-Peer Networking and Applications, 12(2), 493-501.
[CrossRef] [Google Scholar] - Kumar, A., Goyal, S., & Varma, M. (2017, July). Resource-efficient machine learning in 2 kb ram for the internet of things. In International conference on machine learning (pp. 1935-1944). PMLR.
[Google Scholar] - Bolon-Canedo, V., Sanchez-Marono, N., & Alonso-Betanzos, A. (2011). Feature selection and classification in multiple class datasets: An application to KDD Cup 99 dataset. Expert Systems with Applications, 38(5), 5947-5957.
[CrossRef] [Google Scholar] - Li, T., Sahu, A. K., Talwalkar, A., & Smith, V. (2020). Federated learning: Challenges, methods, and future directions. IEEE signal processing magazine, 37(3), 50-60.
[CrossRef] [Google Scholar] - Ring, M., Wunderlich, S., Scheuring, D., Landes, D., & Hotho, A. (2019). A survey of network-based intrusion detection data sets. Computers & security, 86, 147-167.
[CrossRef] [Google Scholar] - Mahmoodi, A. B. Z., Sheikhi, S., Peltonen, E., & Kostakos, P. (2023). Autonomous federated learning for distributed intrusion detection systems in public networks. IEEE access, 11, 121325-121339.
[CrossRef] [Google Scholar] - Conti, M., Dehghantanha, A., Franke, K., & Watson, S. (2018). Internet of Things security and forensics: Challenges and opportunities. Future Generation Computer Systems, 78, 544-546.
[CrossRef] [Google Scholar] - Wohlin, C. (2014, May). Guidelines for snowballing in systematic literature studies and a replication in software engineering. In Proceedings of the 18th international conference on evaluation and assessment in software engineering (pp. 1-10).
[CrossRef] [Google Scholar] - Rahman, S. A., Tout, H., Talhi, C., & Mourad, A. (2020). Internet of Things intrusion detection: Centralized, on-device, or federated learning? IEEE Network, 34(6), 310-317.
[CrossRef] [Google Scholar] - Yang, Q., Liu, Y., Chen, T., & Tong, Y. (2019). Federated machine learning: Concept and applications. ACM Transactions on Intelligent Systems and Technology (TIST), 10(2), 1-19.
[CrossRef] [Google Scholar] - Jiang, C. (2021, November). Efficient quantization techniques for deep neural networks. In 2021 International conference on signal processing and machine learning (CONF-SPML) (pp. 271-277). IEEE.
[CrossRef] [Google Scholar] - Rastegari, M., Ordonez, V., Redmon, J., & Farhadi, A. (2016, September). Xnor-net: Imagenet classification using binary convolutional neural networks. In European conference on computer vision (pp. 525-542). Cham: Springer International Publishing.
[CrossRef] [Google Scholar] - Wang, X., Han, Y., Leung, V. C., Niyato, D., Yan, X., & Chen, X. (2020). Convergence of edge computing and deep learning: A comprehensive survey. IEEE Communications Surveys & Tutorials, 22(2), 869-904.
[CrossRef] [Google Scholar] - Al-Garadi, M. A., Mohamed, A., Al-Ali, A. K., Du, X., Ali, I., & Guizani, M. (2020). A survey of machine and deep learning methods for internet of things (IoT) security. IEEE communications surveys & tutorials, 22(3), 1646-1685.
[CrossRef] [Google Scholar] - Zhang, C., Patras, P., & Haddadi, H. (2019). Deep learning in mobile and wireless networking: A survey. IEEE Communications Surveys & Tutorials, 21(3), 2224-2287.
[CrossRef] [Google Scholar] - Sicari, S., Rizzardi, A., Grieco, L. A., & Coen-Porisini, A. (2015). Security, privacy and trust in Internet of Things: The road ahead. Computer Networks, 76, 146-164.
[CrossRef] [Google Scholar] - De Alwis, C., Porambage, P., Dev, K., Gadekallu, T. R., & Liyanage, M. (2024). A survey on network slicing security: Attacks, challenges, solutions and research directions. IEEE Communications Surveys & Tutorials, 26(1), 534-570.
[CrossRef] [Google Scholar]
Cite This Article
TY - JOUR AU - Patnaik, Phalguni AU - Mishra, Susrita AU - Panda, Bandhan AU - Kar, Santosh Kumar PY - 2026 DA - 2026/03/19 TI - TinyML Driven Intrusion Detection for 5G Network Slices with Leakage-Free Validation JO - Next-Generation Computing Systems and Technologies T2 - Next-Generation Computing Systems and Technologies JF - Next-Generation Computing Systems and Technologies VL - 2 IS - 1 SP - 10 EP - 20 DO - 10.62762/NGCST.2026.664893 UR - https://www.icck.org/article/abs/NGCST.2026.664893 KW - 5G network intrusion detection KW - edge-based ID KW - TinyML for network security KW - leakage-free IDS evaluation KW - feature-pruned machine learning KW - 5G network slicing security AB - The intrusion detection at the 5G network perimeter demands learning frameworks that are practically feasible and computationally efficient. This research proposes a lightweight, slice-sensitive intrusion detection approach designed for edge deployment, with a strong emphasis on minimizing information leakage while accounting for the resource constraints inherent in edge environments. A rigorous chronological and session-discontinuous experimental protocol ensures that training and test traffic remain temporally separated, faithfully replicating realistic deployment conditions. The proposed framework employs a classical Logistic Regression classifier using flow-based statistical features extracted from the 5G-NIDD dataset. To reduce model complexity while preserving detection performance, feature importance-based pruning is applied to retain only the most informative features, followed by post-training INT8 quantization. Rather than focusing on hardware-specific implementations, edge feasibility is assessed through software-based metrics, including model size, computational cost per inference, and CPU inference latency. Experimental results demonstrate that the optimized model exhibits stable intrusion detection performance under leakage-free conditions, achieving results largely comparable to—and in some cases slightly superior to—the full-feature baseline. Notable improvements in memory footprint and computational overhead are achieved, resulting in inference latencies of less than one millisecond in software simulations. Slice-wise analysis reveals predictable and interpretable behavior for both enhanced Mobile Broadband (eMBB) and massive Machine-Type Communications (mMTC) traffic, while conclusions regarding Ultra-Reliable Low-Latency Communications (URLLC) traffic are drawn cautiously due to insufficient representation in the dataset. These findings suggest that carefully constrained classical models, combined with feature-based optimization and strict evaluation protocols, provide a practical and transparent foundation for slice-aware intrusion detection at the 5G edge. SN - 3070-3328 PB - Institute of Central Computation and Knowledge LA - English ER -
@article{Patnaik2026TinyML,
author = {Phalguni Patnaik and Susrita Mishra and Bandhan Panda and Santosh Kumar Kar},
title = {TinyML Driven Intrusion Detection for 5G Network Slices with Leakage-Free Validation},
journal = {Next-Generation Computing Systems and Technologies},
year = {2026},
volume = {2},
number = {1},
pages = {10-20},
doi = {10.62762/NGCST.2026.664893},
url = {https://www.icck.org/article/abs/NGCST.2026.664893},
abstract = {The intrusion detection at the 5G network perimeter demands learning frameworks that are practically feasible and computationally efficient. This research proposes a lightweight, slice-sensitive intrusion detection approach designed for edge deployment, with a strong emphasis on minimizing information leakage while accounting for the resource constraints inherent in edge environments. A rigorous chronological and session-discontinuous experimental protocol ensures that training and test traffic remain temporally separated, faithfully replicating realistic deployment conditions. The proposed framework employs a classical Logistic Regression classifier using flow-based statistical features extracted from the 5G-NIDD dataset. To reduce model complexity while preserving detection performance, feature importance-based pruning is applied to retain only the most informative features, followed by post-training INT8 quantization. Rather than focusing on hardware-specific implementations, edge feasibility is assessed through software-based metrics, including model size, computational cost per inference, and CPU inference latency. Experimental results demonstrate that the optimized model exhibits stable intrusion detection performance under leakage-free conditions, achieving results largely comparable to—and in some cases slightly superior to—the full-feature baseline. Notable improvements in memory footprint and computational overhead are achieved, resulting in inference latencies of less than one millisecond in software simulations. Slice-wise analysis reveals predictable and interpretable behavior for both enhanced Mobile Broadband (eMBB) and massive Machine-Type Communications (mMTC) traffic, while conclusions regarding Ultra-Reliable Low-Latency Communications (URLLC) traffic are drawn cautiously due to insufficient representation in the dataset. These findings suggest that carefully constrained classical models, combined with feature-based optimization and strict evaluation protocols, provide a practical and transparent foundation for slice-aware intrusion detection at the 5G edge.},
keywords = {5G network intrusion detection, edge-based ID, TinyML for network security, leakage-free IDS evaluation, feature-pruned machine learning, 5G network slicing security},
issn = {3070-3328},
publisher = {Institute of Central Computation and Knowledge}
}
Article Metrics
Publisher's Note
ICCK stays neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and Permissions
 Copyright © 2026 by the Author(s). Published by Institute of Central Computation and Knowledge. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/), which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if changes were made.
Copyright © 2026 by the Author(s). Published by Institute of Central Computation and Knowledge. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/), which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if changes were made.

Portico