ICCK Transactions on Information Security and Cryptography | Volume 2, Issue 1: 55-69, 2026 | DOI: 10.62762/TISC.2025.438083
Abstract
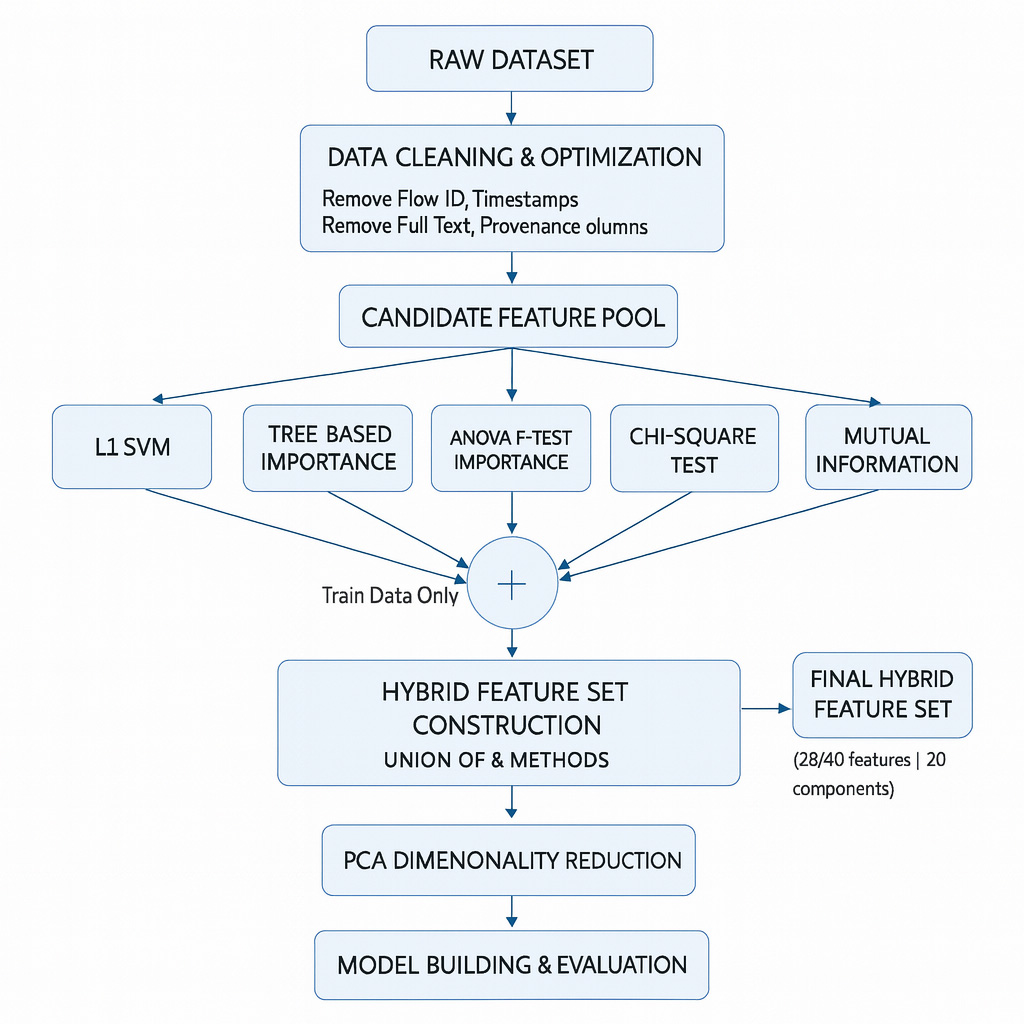
Distributed Denial of Service attacks remain a critical threat to modern networked systems due to their scale, diversity and evolving attack strategies. Although machine learning and deep learning techniques have been widely explored for DDoS detection, many existing studies rely on inconsistent preprocessing pipelines, single-dataset evaluations and limited reproducibility. This work proposes a unified and resource efficient detection framework that addresses these challenges through systematic data handling and transparent model evaluation. The proposed pipeline integrates data cleaning, memory optimization, class balancing and hybrid feature engineering that combines linear, tree-based, s... More >
Graphical Abstract